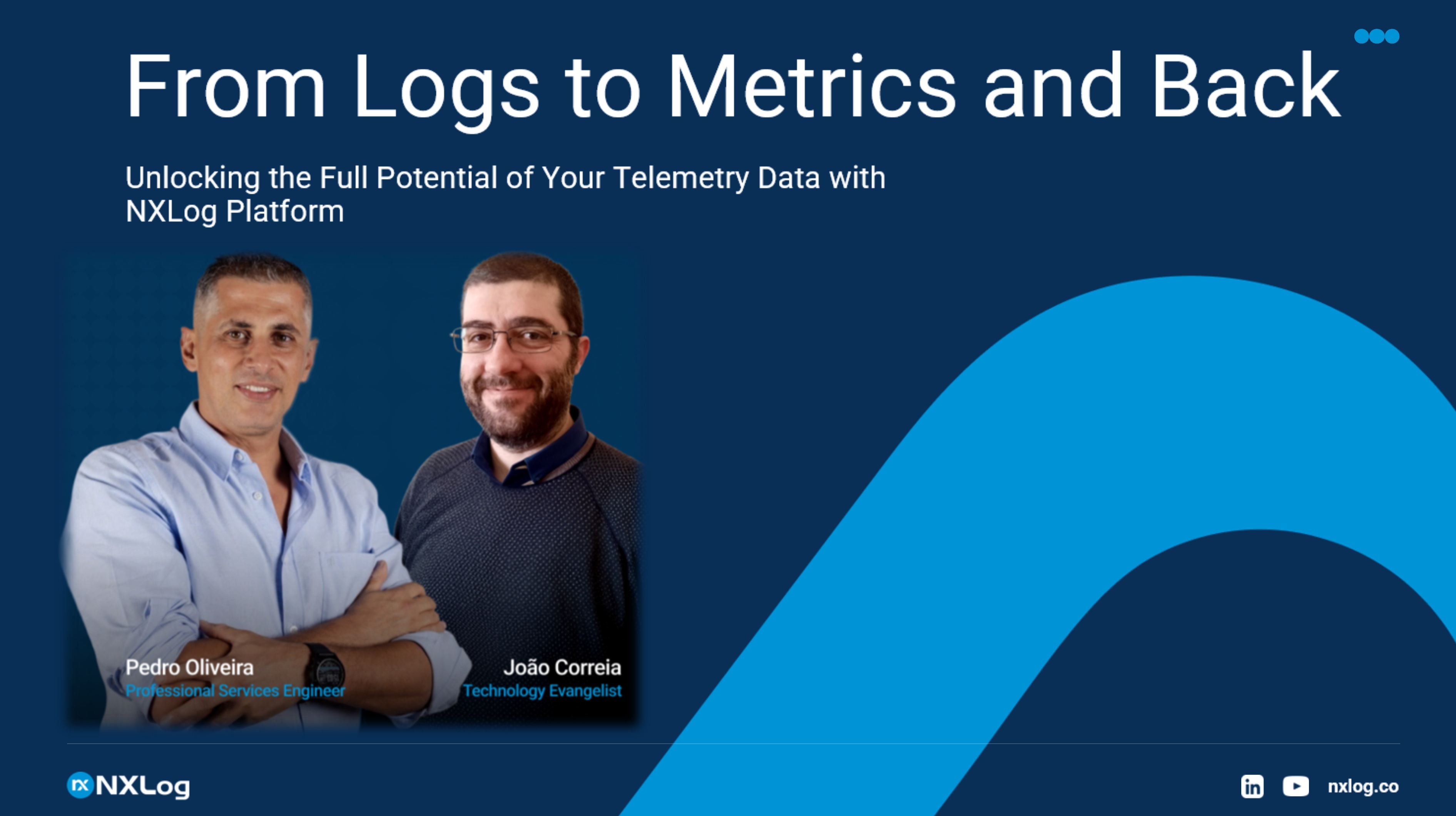
From Logs to Metrics and Back
Your infrastructure generates continuous streams of data — logs, metrics, and traces. But most organizations treat these as separate silos, missing opportunities to extract real business value from information they're already collecting.